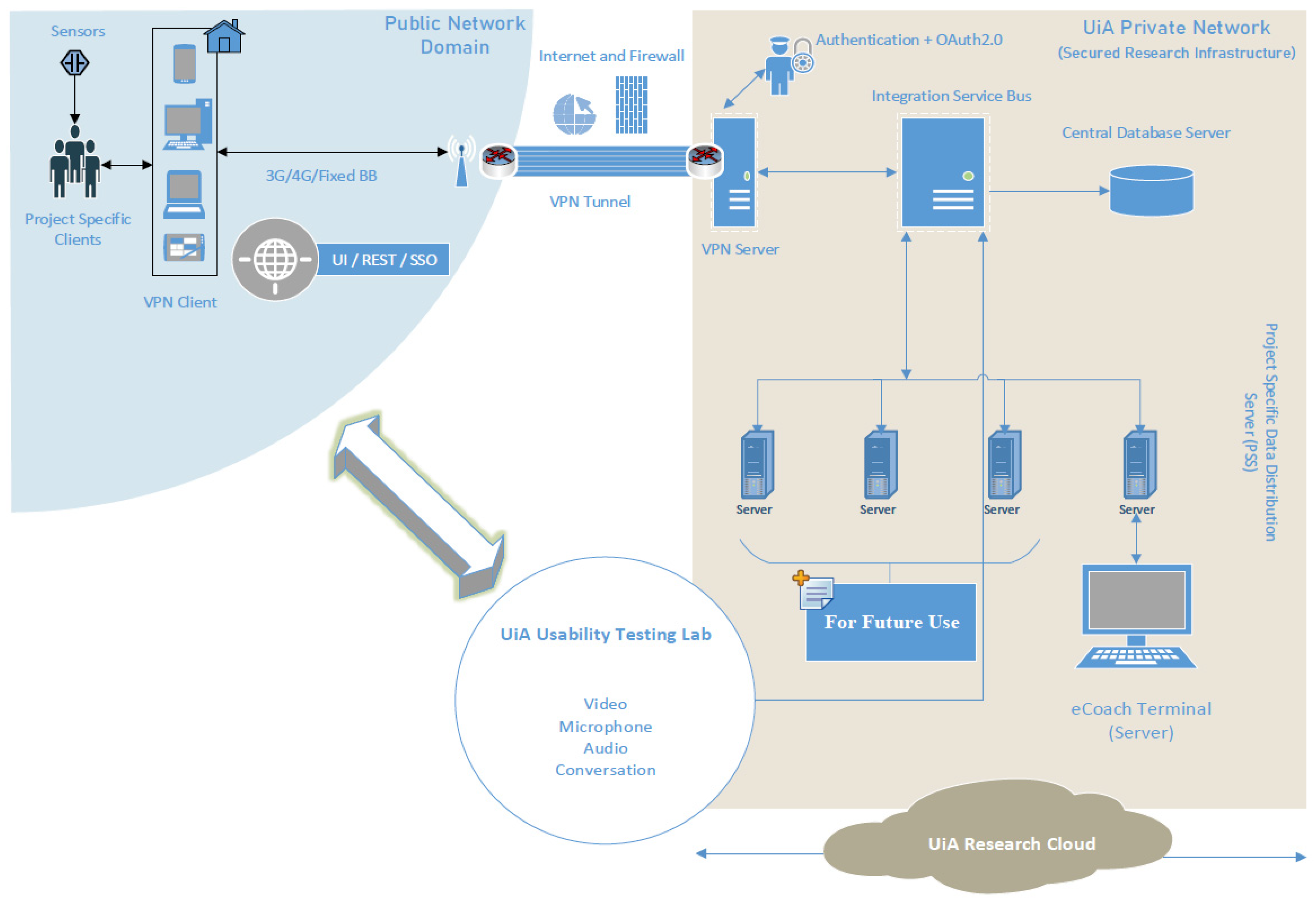
Electronics | Free Full-Text | VaultPoint: A Blockchain-Based SSI Model that Complies with OAuth 2.0
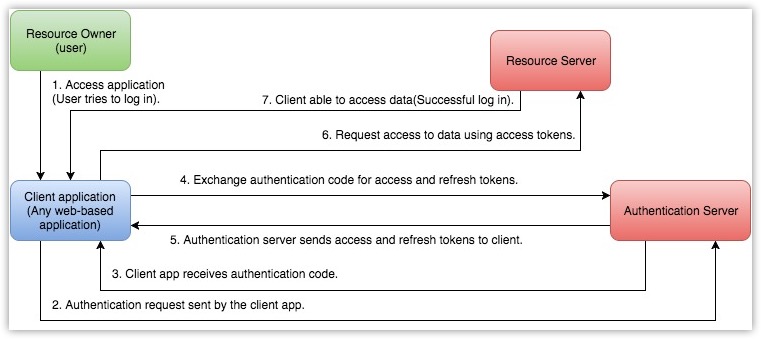
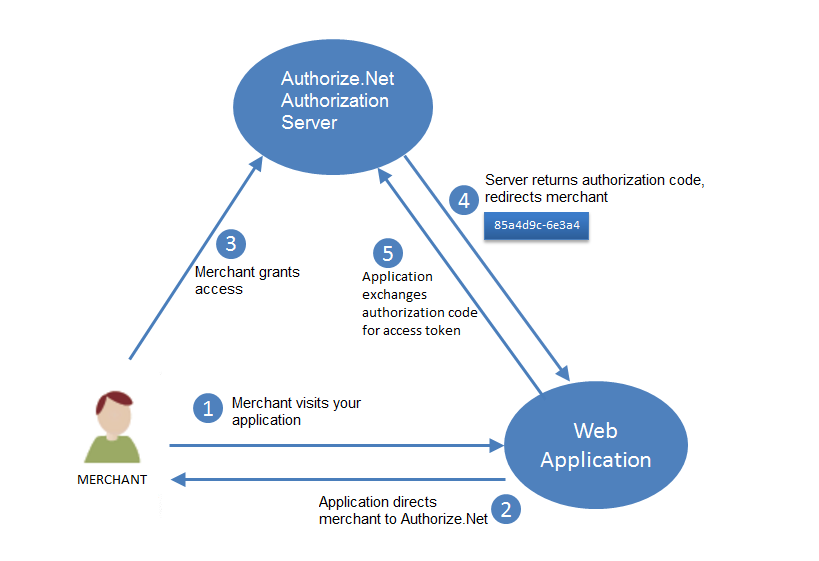
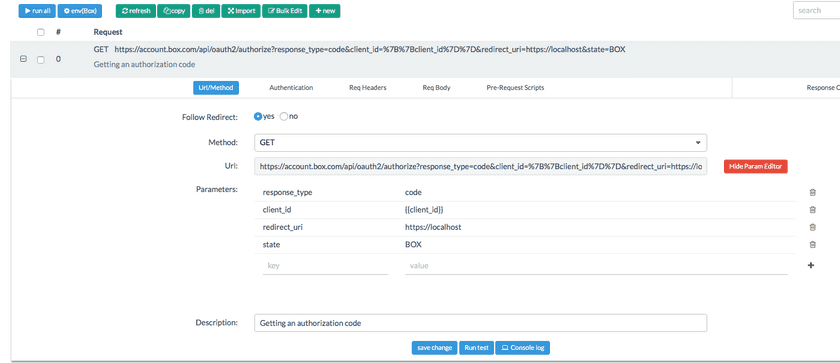
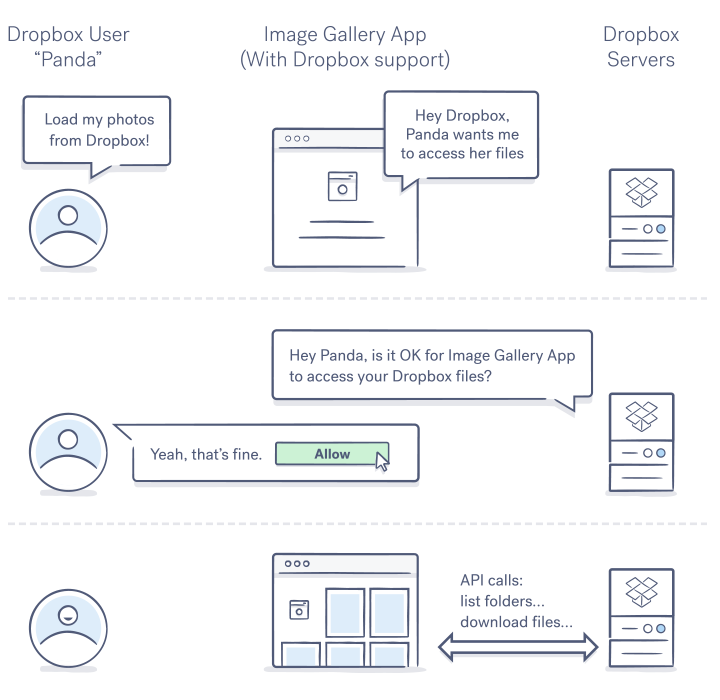
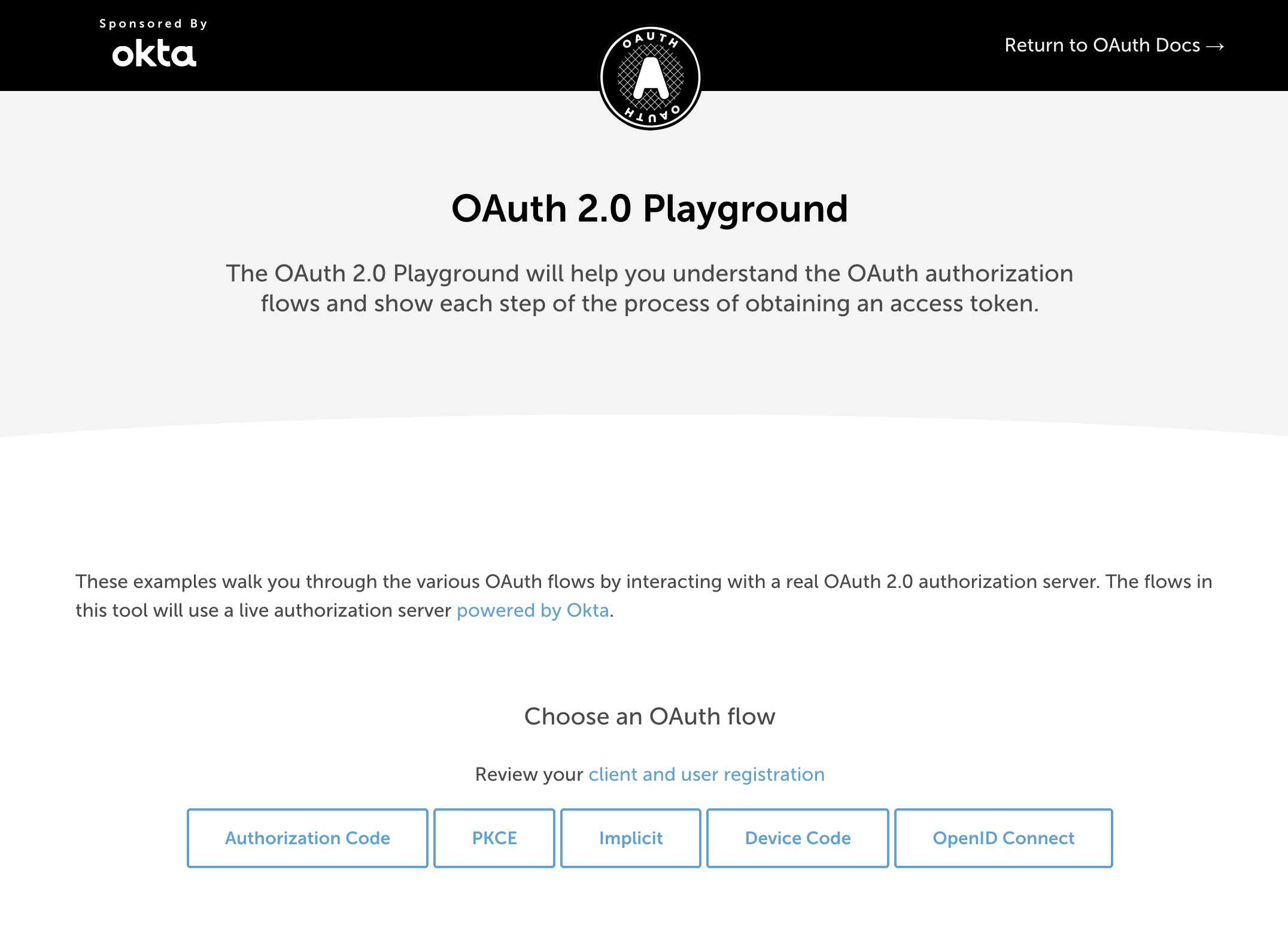
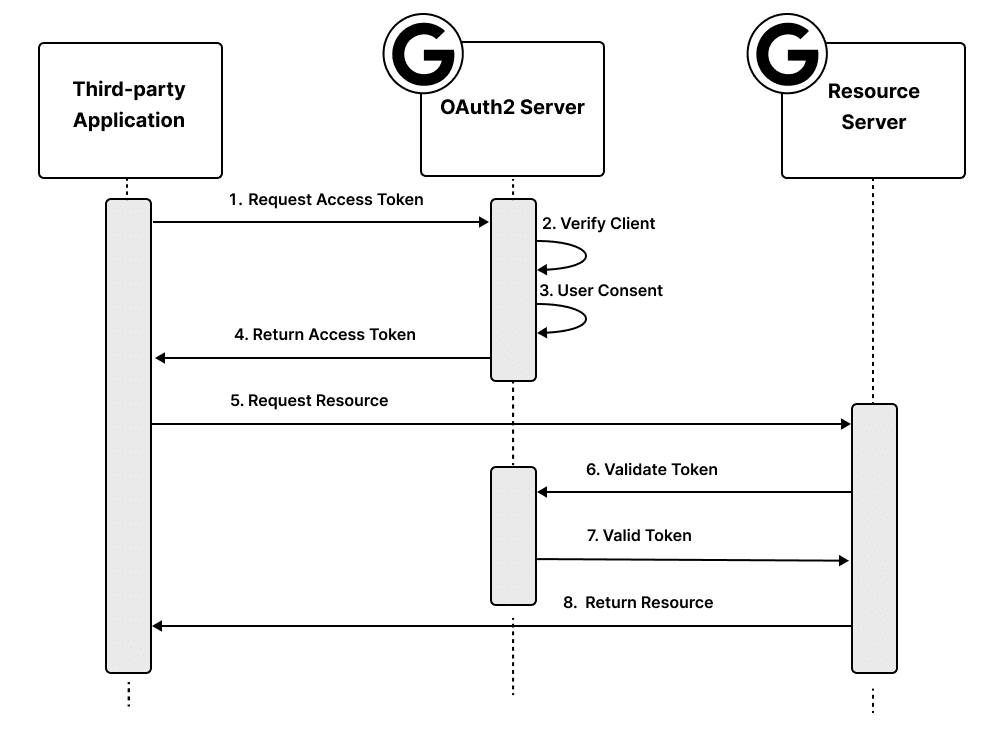
Understanding OAuth2 and Building a Basic Authorization Server of Your Own: A Beginner's Guide | by Ratros Y. | Google Cloud - Community | Medium

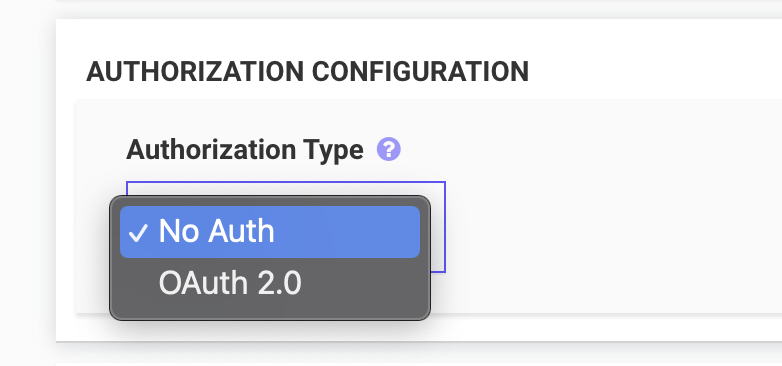
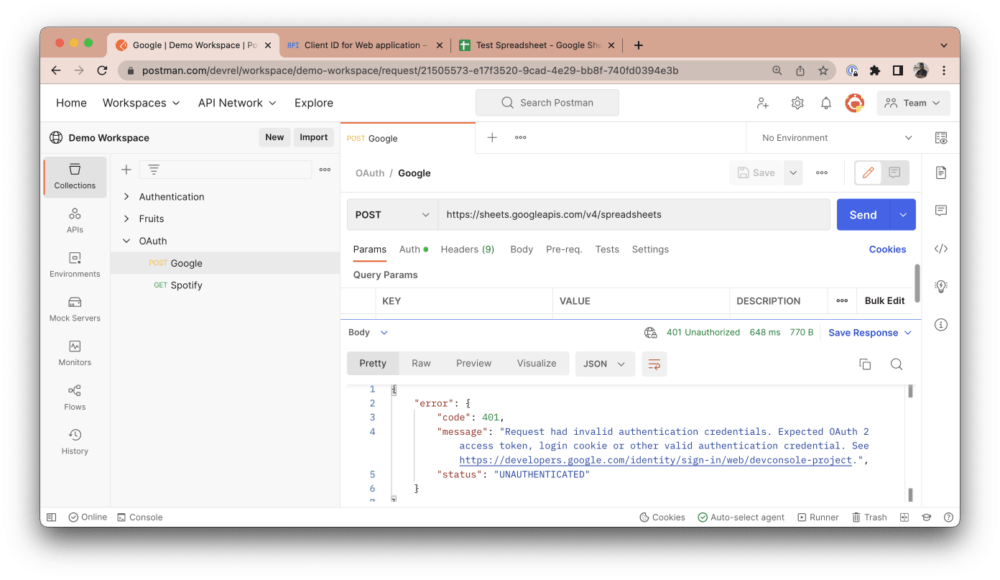
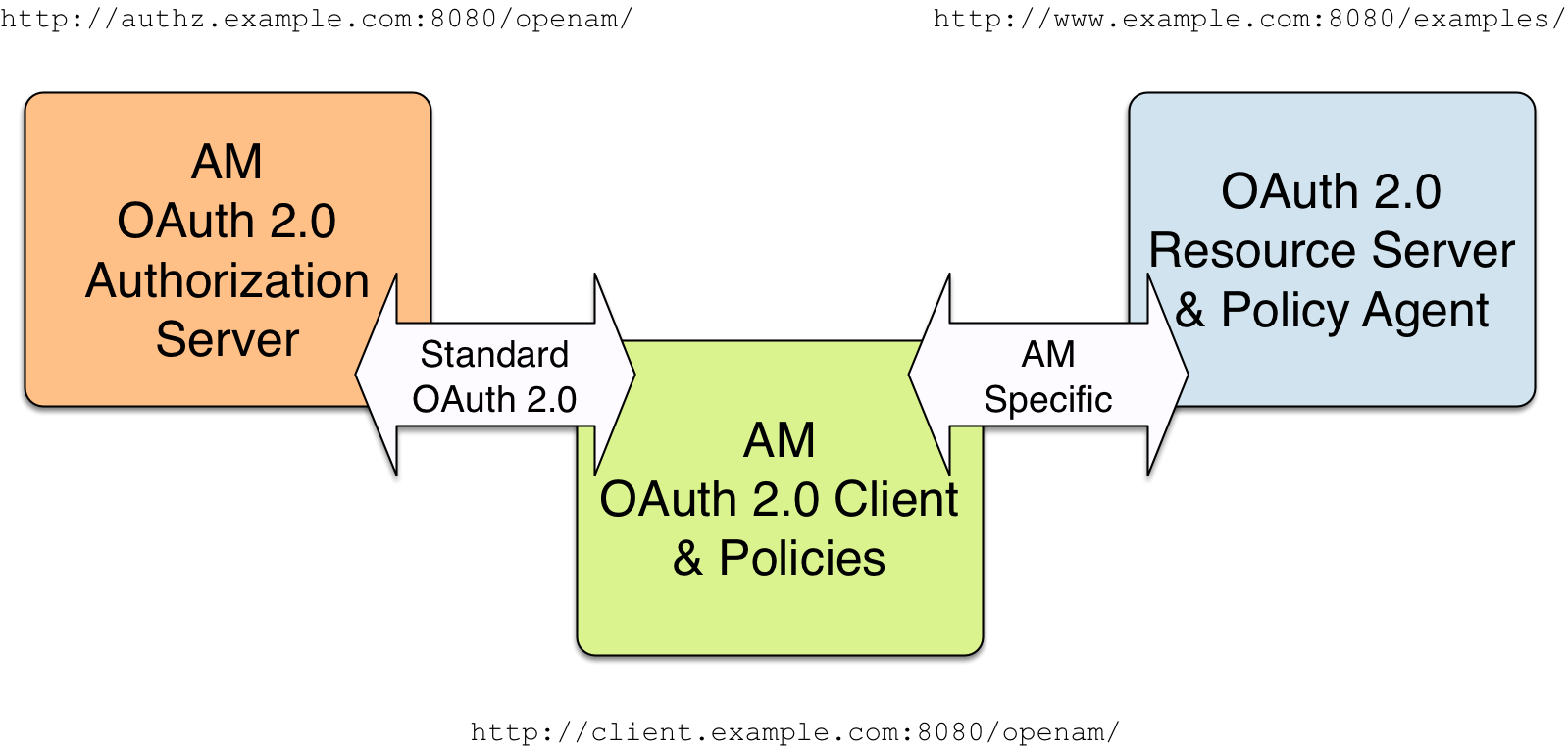
Consuming an endpoint protected by an OAuth 2 resource server from a Spring Boot service – LaurSpilca